Download Password protected modular computer method and device
Transcript
USO0RE41294E
(19) United States
(12) Reissued Patent
(10) Patent Number:
US RE41,294 E
(45) Date of Reissued Patent:
*Apr. 27, 2010
Chu
(54)
PASSWORD PROTECTED MODULAR
COMPUTER METHOD AND DEVICE
(75)
Inventor:
5,103,446 A
5,191,581 A
5,251,097 A
William W. Y. Chu, Los Altos, CA (US)
(73) Assignee: ACQIS Techonology, Inc., Mountain
View, CA (US)
(*)
Notice:
This patent is subject to a terminal dis
claimer.
(51)
Issued:
Nov. 20, 2001
Appl. No.:
09/183,493
Filed:
Oct. 30, 1998
web on Jun. 23, 2004, 3 pgs.
“SQL Server and NT Cluster Manager Availability Demo,”
Microsoft Server Programmer Developers Conference, Nov.
1996, 15 pages total.
Agerwala, T., Systems Journal “SP2 System Architecture”
Int. Cl.
vol. 34, No. 2, 1995 Scalable Parallel Computing vol. 34,
No. 2, 1995.
(Continued)
US. Cl. .......................... .. 713/193; 710/301; 726/9;
726/18; 726/28
(58)
Field of Classi?cation Search ................ .. 713/164,
Primary ExamineriBeemnet W Dada
(74) Attorney, Agent, or FirmACooIey Godward Kronish
713/172, 189, 190, 194, 193; 711/164; 710/100,
LLP
710/301; 726/2, 9, 17, 18, 19, 20, 28; 361/687
See application ?le for complete search history.
(57)
(56)
puter Module Bay (“CMB”) 40 within a peripheral console
U.S. PATENT DOCUMENTS
>
12/1976
11/1986
10/1987
9/1988
10/1989
12/1989
4/1990
7/1990
10/1991
2/1992
ABSTRACT
A method and device for securing a removable Attached
Computer Module (“ACM”) 10. ACM 10 inserts into a Com
References Cited
3,996,585
4,623,964
4,700,362
4,769,764
4,872,091
4,890,282
4,918,572
4,939,735
5,056,141
5,086,499
7/1996
10/1994
10/1992
1/1994
5/1995
1/1997
mes.com/testing/97feb/702b072a.html>>, downloaded from
(2006.01)
(52)
722138 A1
6-289953
WO 92/18924
WO 94/00097
WO 95/13640
WO97/00481
“Features Chart”, (Feb. 1, 1997) <<http://www.lanti
Related US. Patent Documents
6,321,335
EP
JP
W0
W0
W0
WO
OTHER PUBLICATIONS
Reissue of:
Patent No.:
(Continued)
FOREIGN PATENT DOCUMENTS
(21) Appl. No.: 11/474,256
Jun. 23, 2006
(22) Filed:
(64)
4/1992 Fischer
3/1993 Woodbury et 31.
10/1993 Simmons et a1.
to form a functional computer such as a desktop computer or
Hogan
portable computer. The present ACM 10 includes a locking
system, which includes hardware and software 600, 700, to
GetZ et 31.
Todd et a1.
Levanon
Maniwa et a1.
Lambert et a1.
Tarver et a1.
Fredericks et a1.
prevent accidental removal or theft of the ACM from the
peripheral console. While ACM is in transit, further security
is necessary against illegal or unauthorized use. If ACM con
tains con?dential data, a high security method is needed to
safeguard against theft.
Dyke
Mutone
36 Claims, 12 Drawing Sheets
ATTACHED COMPUTER MODULE
e
527
529,”; MiélllgR‘l
CPU ‘L. g?ggg
CPU
|
'
Bus
R
comer.
sax-P
FLASH MEM 1% 505
WITH BIOS a
HOEJSPCI
533
USER
PASSWORD
I
IEORST |__-\.510
FT- CONTROLLER
INT FACE
\
LOCK CONTROL
INTERFACE
CONNECTORS
US RE41,294 E
Page 2
US. PATENT DOCUMENTS
5,278,509 A
5,278,730 A
5,293,497 A
1/1994 Haynes etal.
V1994 Kikinis
3/1994 Free
5,311,397 A
5,317,477 A
5,319,771 A
5/1994
5/1994
6/1994
7/1994
10/1994
6/1995
7/1995
10/1995
5/1996
7/1996
8/1996
5,331,509 A
5355391
5,428,806
5436857
5,463,742
5,519,843
5,539,616
5,550,710
5,550,861
5,572,441
5,578,940
5,600,800
5,603,044
5,606,717
5,608,608
A
A
A
A
A
A
A
A
A
A
A
A
A
A
5,623,637 A
4/2000
5/2000
5/2000
7/2000
7/2()()()
8/2000
MacLaren
Abraham et a1.
Ahern
Gallagher et a1.
Ahem
Cosleyetal.
12/2000 Gallagher et a1.
6,163,464
6,175,490
6,202,169
6,208,522
6,216,185
6,256,689
6,260,155
6,266,539
6,289,376
6,304,895
6,311,268
6,314,522
6,317,329
6,321,335
A
B1
B1
B1
B1
B1
B1
B1
B1
B1
B1
B1
B1
B1
12/2000
1/2001
3/2001
3/2001
4/2001
7/2001
7/2001
7/2001
9/2001
10/2001
10/2001
11/2001
11/2001
11/2001
Ishibashietal.
Papa et al.
RaZZaghe-Ashra? et a1.
Manweileretal.
Chu
Khosrowpour
Dellacona
Pardo
Tayloretal.
Schneider etal.
Chu
Chu et a1.
Dowdy etal.
Chu
4/1997 Jones et a1. ............... .. 711/164
6,332,180 B1
l2/200l
Kauffman et 31‘
5/1997 Hair
6/1997 Buchalaet al.
6,345,330 B2
6,366,951 B1
2/2002 Chu
4/2002 Schmidt
2/1997
2/1997
2/1997
3/1997
Kikinis et 31.
Annapareddy eta1~
Farmwaldet a1~
Flintet 31.
6/1997 Kikinis ..................... .. 361/687
6,378,009 B1
4/2002 Pinkston, H et 31‘
5,648,762 A
7/1997 lchimum er 91-
6,381,602 B1
4/2002 Shoroffetal.
5,659,773 A
8/1997 Huynh eta1~
6,393,561 B1
5,663,661
5,673,174
5,680,126
5689654
5,721,837
5,721,842
5,745,733
5,751,711
5,752,080
5,764,924
5,774,704
5,795,228
5,809,538
5,815,681
5,819,050
5,826,048
5,838,932
*
6,052,513 A
6,069,615 A
6,070,214 A
6,157,534 A
8/1996 Chan et al.
*
3/2000 Watson et a1.
4/2000 Bovio et al.
6,088,224 A
6,088,752 A
6,104,921 A
11/1996 Boie
11/1996 Dillon
5,630,057 A
5,638,521 A
5,640,302 A
HarshbergeretalGillett
Takeda
Kikinis
HOIOWIIZ etal
Poems
Nelson et a1~
Kobayashi
Moran etal.
Kikinis
R?hamim eta1~
6,040,792 A
6,046,571 A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
A
9/1997
9/1997
10/1997
11/1997
2/1998
2/1998
4/1998
5/1998
5/1998
6/1998
6/1998
8/1998
9/1998
9/1998
10/1998
10/1998
11/1998
5,848,249 A
’
6,401,124
6,425,033
6,452,789
6,452,790
6,453,344
6,496,361
6,549,966
6,564,274
6,643,777
6,718,415
6,725,317
7,099,981
7,146,446
2001/0011312
gin“? 1
5/2002 Hagiwaraetal.
B1
B1
B1
B1
B1
B2
B1
B1
B1
B1
B1
B2
B2
A1
6/2002
7/2002
9/2002
9/2002
9/2002
12/2002
4/2003
5/2003
11/2003
4/2004
4/2004
8/2006
12/2006
8/2001
Yang etal‘
Conway et a1.
Pallotti et a1.
Chu et a1.
Ellsworth
Kimetal.
Dickens et a1.
Heath et a1.
Chu
Chu
Bouchieretal.
Chu
Chu
Chu
OTHER PUBLICATIONS
12/1998 Gums
i *
’
Dillon et al.
Hamirani
Kikinis
Kikinis
Kikinis
Beasleyetal'
Robinson
Sakaue
Ryan
H9118
Williams
Trumbull
Pollmann
Kikinis
Boehling et 211.
Dempsey et a1.
AlZien
Bemal, Carlos, product brochure entitled: “PoWerSMP
717/125
Vameta' """"""" "
Series 4000”, (Mar. 1998) <<http://WWW/Winnetmag,com/
WindoWs/Article/Article1D/3095/3095.html,
downloaded
5,907,566 A
5,933,609 A
5/1999 Benson et 31.
8/1999 Walker et a1.
from Web on 1119223200432 Pgs'
5,941,965 A
5,948,047 A
5,960,213 A
8/1999 MoroZ
9/1999 Jenkins et a1.
9/1999 Wilson
CETIA Brochure “CETIA PoWerengine CVME 603e” pp.
1A6 doWnloaded from the internet at. http://WWW.cetia.com/
ProductAddOns/WpA47A01.pdf on Feb. 15, 2006.
gillljghztrllt'al‘
5,977,989 A
5,978,919 A
5,982,363 A
2733i’
,
11/1999 Lee et a1‘
* 11/1999 Doietal. .................... .. 726/36
11/1999 Naiff
2
Efrem“ et 31'
,
Cragle, Jonathan, “Density System 1100i’, May‘ 1999)
<<http://WWW.W1nnetmag.com/W1ndoWs/Art1cle/Art1cle1D/
5199/5199~hIm1>>, downloaded from Web 011 Jun-21, 2004,
3pgs.
Crystal Advertisement for “QuickConnect® Cable Manage
osroWpour
”
5,999,952 A * 12/1999 Jenkins etal. ............ .. 708/100
.
_
{11230111322202
Li et a1.
‘1
'
sijigc'ocno?mlg
6,002,442 A
12/1999
6,003,105 A
12/1999 Vicard et a1.
2004,4Pgs
P
'
’
6,006,243 A
6,009,488 A
12/1999 Karidis
12/1999 KaViPumPu
Crystal Advertisement for “Rackmount Computers”, (@
2000A2004) <<http://WWW.crystalpc.com/products/roserv
6,011,546 A
V2000 Bertram
6,012,145 A
1/2000
6,016,252 A
6,028,643 A
V2000 pignolet et a1‘
2/2000 Jordan et a1‘
Cub1x Product Brochure ent1tled, Density System , (@
2000) <<http://64.173.211.7/support/techmfo/system/den
6,()29,1g3 A
6,038,621 A
2/2()()() Jenkins et a1,
3/2000 Gale et a1.
sity/densityl0.htm>> downloaded from Web on Jun. 22,
2004, 3 pgs.
Mathers et al.
ers.asp>>, doWnloaded from Web on Jun. 17, 2004, 8 pgs.
.
.
“
.
,,
US RE41,294 E
Page 3
Cubix Product Brochure entitled, “Density System, Techni
eBay Advertisement for “Total IT Group Network Engines”,
cal Speci?cations”, (@ 2000) <<http://64.173.211.7/support/
<<http://cgi.ebay.com/we/eBayISAPI.dll?ViewItem&item=
5706388046&sspagename+STRK%3AMDBI%
techinfo/system/density/info/spec.htm>> downloaded from
Cubix Product Manual entitled, “Density System”, Chapter
3MEBI3AIT&rd=1>>, downloaded from web on Jun. 25,
2004, 1 pgs.
1*Introduction, (@ 2000) <<http://64.173.211.7/support/
Eversys Corp. “Eversys System 8000 Consolidated Network
techinfo/manuals/density/Chapi1.htm>> downloaded from
Server Market and Product Overview,” Slide Presentation,
downloaded from <<http://eversys.com>>, 20 pages total.
web on Jun. 22, 2004, 2 pgs.
web on Jun. 22, 2004, 5 pgs.
Cubix Product Manual entitled, “Density System”, Chapter
2*Installation, (@ 2000) <<http://64.173.211.7/support/
techinfo/manuals/density/Chapi2.htm>> downloaded from
web on Jun. 22, 2004, 9 pgs.
Cubix Product Manual entitled, “Density System”, Chapter
3*Operation, (@ 2000) <<http://64.173.211.7/support/
techinfo/manuals/density/Chapi3.htm>> downloaded from
web on Jun. 22, 2004, 4 pgs.
Cubix Product Manual entitled, “Density System”, Chapter
4*Maintenance and Repair, (@ 2000) <<http://64.173.211.7/
support/techinfo/manuals/density/Chapi4.htm>>
down
Feldman, Jonathan, “Rack Steady: The Four RackiMounted
Servers That Rocked Our Networ ”, <<http://www.net
workcomputing.com/shared/printArticlejhtml?article=/
910/910r3side1.htm...>> Jun. 23, 2004, 3 pg.
Fetters, Dave, “Cubix HighiDensity Server Leads the Way
With Standout Management Software”, (Feb. 8, 1999)
<<http://www.nwc.com/shared/printArticle.jhtml?article=/
1003/1003r3full.html&pub=nwc>>, downloaded from web
on Jun. 23, 2004, 5 pgs.
Gardner, Michael and Null, Christopher, “A Server Condo
loaded from web on Jun. 22, 2004, 5 pgs.
minium”,
Cubix, “Click on the front panel that matches your system”,
806a042a.html>>, Jun. 23, 2004, 3 pgs.
Harrison, Dave, “VME in the Military: The M1A2 Main
(@ 2000) <<http://64.173.211.7/support/techinfo/system/
density/density.htm>> downloaded from web on Jun. 22,
2004, 1 pg.
Cubix, “DP 6200 ‘D’ Series Plugiin Computers” <<http://
64.173.21 1.7/support/techinfo/bc/dp/6200d/intro.htm
>>,
downloaded from web on Jun. 22, 2004, 2 pgs.
Cubix, “Installing DP or SP Series Boards”, (@ 2000)
<<http ://www.lantimes.com/testing/98jun/
Battle Tank Upgrade Relies on COTS VME” <<http://
www.dy4.com>>, (Feb. 9, 1998), pp. 1434.
Internet Telephone Roundup, “Industrial Computers”,
<<http://www.tmcnet.com/articles/itmag/0499/0499round
up.htm>>, downloaded from web on Jun. 23, 2004, 5 pgs.
Microsoft Cluster Service Center, “MSCS Basics,” down
<<http://64 . 1 73 .21 1 .7/support/techinfo/system/density/info/
loaded from <<http://www.nwnetworks.com/mscsbasics.
pic*inst.htm">> downloaded from web on Jun. 22, 2004, 2
htm>>, Feb. 7, 2005, 4 pages total.
MPL Brochure, “1st Rugged All in One Industrial
P85
Cubix, “Multiplexing Video, Keyboard & Mouse with Mul
tiple Density Systems”, (@ 2000) <<http://64.173.211.7/
support/techinfo/ system/density/info/vkmimux .htm>>
downloaded from web on Jun. 22, 2004, 2 pgs.
Cubix, “Powering On/Off or Resetting Plugiin Computers
in an Density System”, (@ 2000) <<http://64.173.211.7/sup
port/techinfo/system/density/info/power.htm>> downloaded
486FDX*133 MHZ PC” pp. 142, downloaded from the inter
net at. http://www.mpl.ch/DOCs/ds48600.pdf on Feb. 15,
2006.
MPL Brochure “IPM 486 Brochure/IPM5 User Manual” pp.
149 downloaded from the Internet at http://www.mpl.ch/
DOCs/u48600xd.pdf on Feb. 15, 2006.
Cubix, “SP 5200 Series”Chapter 1*Introduction, (@ 2000)
MPL, “The First Rugged AlliiniOne Industrial
486FDX*133 MHZ PC”, IPM486/IPM5 User Manual, 1998,
<<http:// 64.173 .21 1 .7/ support/techinfo/manuals/ sp5200/
pp. 1452.
from web on Jun. 22, 2004, 2 pgs.
chap*1.htm>>, downloaded from web on Jun. 22, 2004, 3
Press Release: Hiawatha, Iowa, (Mar. 1, 1997) entitled
Pg
“Crystal Group Products Offer Industrial PCs with Builtiin
Cubix, “SP 5200 Series”Chapter 2*Switches & Jumpers, (@
Flexibility”,
2000)
leases/prodpr.asp>>, downloaded from web on May 14,
2004, 2 pgs.
<<http://64.173.211.7/support/techinfo/manuals/
sp5200/chap*2.htm>>, downloaded from web on Jun. 22,
2004, 3 pgs.
Cubix, “SP 5200 Series”Chapter 3*Installation, (@ 2000)
<<http:// 64.173 .21 1 .7/ support/techinfo/manuals/ sp5200/
<<http://www.crystalpc.com/news/pressre
Press Release: Kanata, Ontario, Canada, (Apr. 1998) entitled
“Enhanced COTS SBC from DY 4 Systems features
166MHz PentiumTM Processor” <<http://www.realtime*in
chap*3.htm>>, downloaded from web on Jun. 22, 2004, 4
fo.be/VPR/layout/display/pr.asp?/pr.asp?PRID=363>>,
pgs.
pgs.
Product Brochure entitled: “SVME/DMil92 Pentium® II
Cubix, “SP 5200 Series”Chapter 4*Technical Reference, (@
2000)
<<http://64.173.211.7/support/techinfo/manuals/
sp5200/chap*4.htm>>, downloaded from web on Jun. 22,
2004, 3 pgs.
2
Single Board Computer” (Jun. 1999) pp. 149.
Product Brochure entitled: “System 8000”, <<http://www.
bomara.com/Eversys/briefDefault.htm>>, downloaded from
Cubix, “SP 5200XS Series Plugiin Computers”, (@ 2000)
<<http:// 64.173 .21 1 .7/ support/techinfo/bc7/ sp5200Xs/in
web on Jun. 22,2004, 4 pgs.
tro.htm>>, downloaded from web on Jun. 22, 2004, 2 pgs.
Product Brochure entitled: “ERS/FT II System”, (@ 2000)
Cubix, “SP 5200XS Series Technical Speci?cations”, (@
<<http://64.173.21 1.7/support/techinfo/system/ersft2/
2000) <<http://64.173.211.7/support/techinfo/bc/sp5200Xs/
ersft2.htm>>, downloaded from web on Jun. 22, 2004, 4 pgs.
Product Manual entitled: “ERS II and ERS/FT II”, Chap. 3,
spec.htm>>, downloaded from web on Jun. 22, 2004, 2 pg.
64 . 1 73 .21 1.7/support/techinfo/system/density/info/group
System
Components,
<<http:// 64.173 .21 1 .7/ support/
techinfo/manuals/ers2/ers2ic3.htm>>, downloaded from
s.htm>>, downloaded from web on Jun. 22, 2004, 3 pgs.
web on Jun. 22, 2004, 22 pgs.
Cubix,
“What are Groups?”,
(@
2000)
<<http://
US RE41,294 E
Page 4
Product Manual entitled: “ERS H and ERS/FT ll”, Chap. 6,
WindoWs Magazine, “Cubix PoWerSMP Series 4000”, Nov.
Component Installation, <<http://64.173.211.7/support/
1997,
techinfo/manuals/ers2/ers2ic6.htm>>, downloaded from
1101/ntent008.htm>> doWnloaded from the Web on Jun. 22,
Web on Jun. 22, 2004, 18 pgs.
Synder, Joel “Better Management through consolidation’
<http://WWW.techWeb.com/Winmag/library/1997/
2004, p. NT07.
a
pp. 146 doWnloaded from the internet at http://
WWW.opus 1 .COIn/WWW/jInS/nW*COI1*081 8rev.html.
U.S. Appl. No. 12/322,858 ?led Feb. 5, 2009, Chu, William
Williams, Dennis, “ChatCom Inc. Chatterbox”, (Feb. 17,
Dirk S. Faegre et al., “CTOS Revealed”, http://WW.byte<
1997)
<<http://WWW.lantimes.com/testing/97feb/
702b066ahtml>> doWnloaded from Web on Jun. 23, 2004, 3
pgs.
Williams, Dennis, “Consolidated Servers”, (Feb. 17, 1997)
<<http://WWW.lantimes.com/testing/97compare/pccon
sol.html>> doWnloaded from Web on Jun. 23, 2004, 2 pgs.
Williams, Dennis, “Cubix Corp. ERS/FTH”, (Feb. 17, 1997)
<<http://WWW.lantimes.com/testing/97feb/
702b068b.html>> doWnloaded from Web on Jun. 23, 2004, 4
Pg5~
W.Y.
com/art/9412/sec13/art2.htm.
Jesse Berst’s Anchor Desk, http://WWW.Zdnet.com/an
chordesk/talkback/talkbacki5 6 5 5 5 .html.
Jesse Berst’s Anchor Desk, http://WWW.Zdnet.com/an
chordesk/story/storyil 504.html.
Kelly Spang, “Component House: Design Technology for
PCs in a snap’iNeoSystmes Offers Building Blocks”,
Williams, Dennis, “EVERSYS Corp. System 8000”, (Feb.
Computer Reseller NeWs, Apr. 21, 1997, Issue 732, Section:
Channel
Assembly,
http ://WWW.techWeb.com/se/
17,
directlink.cgi?CRN1 9970421 S0054.
1997)
<<http://WWW.lantimes.com/testing/97feb/
702b070b.html>> doWnloaded from Web on Jun. 22, 2004, 4
Pg5~
Williams, Dennis, “Executive Summary: Consolidate NoW”,
(Feb. 17, 1997) <<http://WWW.lantimes.com/testing/97feb/
702b064a.html>> doWnloaded from Web on Jun. 23, 2004, 2
Pg5~
Williams, Dennis, Top “Scores for Useability and Open
Rick BoydiMerritt, “UngradeableiPC effort takes divergent
paths”,
http://techWeb.cmp.com/eet/neWs/97/949neWs.ef
fort.html.
“Think Modular”, PC MagaZine, Jun. 10, 1997, WysiWyg://
60http://homeZdnet.com/pcmag/issues/1611/
pcmg0072.htm.
ness”, (Feb. 17, 1997) <<http://WWW.lantimes.com/testing/
97feb/702b070a.html>> doWnloaded from Web on Jun. 23,
2004, 2 pgs.
* cited by examiner
US. Patent
Apr. 27, 2010
COMPUTER
MODL?bE BAY
Sheet 1 0f 12
US RE41,294 E
MONITOR
DESKTOP
PERIPHERAL
CON2%OLE
1°
ATTACHED
COMPUTER
MODULE
FIG.1
US. Patent
Apr. 27, 2010
Sheet 2 0f 12
US RE41,294 E
ACM ENCLOSURE
OPENING FOR
ENGAGING LOCK
FIG.2
US. Patent
Apr. 27, 2010
Sheet 3 0f 12
US RE41,294 E
10
W
26
FRONT
17
21
MANUAL KEY
RELEASE
{E033
11 1:24
/
INSERTION
BLOCKED
\
“
29
<
23
A
'
r‘
PEFQIPHERAL
mcgyuiléTsE/gr
CONSOLE
FRAME
ENCLOSURE
US. Patent
Apr. 27, 2010
US RE41,294 E
Sheet 4 0f 12
17
_
CMI CONNECTOR
__
CMI CONNECTOR
iI
i
I
I
I
I
I
I
1I
I
7I';
I
Il
\ POWER
REGULATOR
MAIN CIRCUIT
I-__ /BOARD
431
\1 432 I
[1]
COMPONENT
UNDERNEATH
I
'
I
I CONNECTION T0
i /LOCK CONTROL
i
L
'IDECON. ]—---~__.__.
2427
FIG.4
SECURITY
LOCK
15
US. Patent
Apr. 27, 2010
Sheet 5 0f 12
US RE41,294 E
//500
501
ATTACHED COMPUTER MODULE
J
I
523
PRIMARY HARD DISK
wI SECURITY
PROGRAM
MAIN
502-1-
MEMORY
525
e
CPU
—
(I
‘
E
L~ I] BUS
537
a
EQFDQTGPE
CPU
‘
_ HDD CONTROLLER
53‘
' “0&5?
GRAPHICS
SUBSYSTEM
‘r
SEFOJCRRTY
519
WITUSBEIQSSI
_
PASSWORD
@I _L
'
A
=
)
l
FLASH MEM ‘@505
CONTROL 1533
=
543w
515
N503
Y
"L541
526
521
BUS
‘
529O~ MEéIAgRY 2
527
DRIVE
HOST '———'“‘-51°
INTERFACE
\\
CONTROLLER
535
\\ 511
LOCK CONTROL
3
v
i
509
5”
VIDEO
507
513
I
INTERFACE
CONNECTORS
US. Patent
Apr. 27, 2010
Sheet 6 0f 12
US RE41,294 E
f/ 500
ATTACHED COMPUTER MODULE
PROGRAM
x 501
DRIVE
,
A
BUS
= HDD CONTROLLER r‘C503
q.
FLASH MEM
533
H
0355"‘
wLTLLJTSEggs & V505
PASSWORD
507
l
-
~
[J
HOST INTERFACE CONTROLLER
LOCK ONIOFF LOCK STATUS
SOLENO")
DRLVER
SECURITY
| T
LOCK
CONTROL BIT
\ 551
J--\---'
(
f
557 553 LOCK STATUS SIGNAL
GND
559
FIG.5A
BIT \
L 549
509
551
Mcc
US. Patent
Apr. 27, 2010
Sheet 7 0f 12
ACM INSERTED
INTO CMB
600
US RE41,294 E
ACM OUTSIDE OF
CMB
)A/
SECURITY
701
USE KEY
PROGRAM “\- 603
6
/
TO PREVENT
ILLEGAL USE
( POWER UP h. 601
700
TO TURN ""1- 703
LOCK ON
014
605
NO
_\- 705
7
LOCK
STAYS OFF
2609
INTO CMB
YES
606
SOFTWARE
TURNS
LOCK 0N
I 607
T
USE KEY
TO TURN
LOCK OFF
E
61% OS TURNS
POWER
‘366%;
FAILURE
Y
@611
ACM CAN
INSERT
\
e17
UEEL'EEAYSTEO
'
LOCK
LOCK
STAYS ON
622
621
‘\ NO
‘7
STLAQWON
1S
62‘
‘I
ACM CAN
BE
REMOVED
627
—\_ s15
CMB
1 709
FIG.7
US. Patent
Apr. 27, 2010
Sheet 9 0f 12
+
PCK
+
—— Driver
--—-
Driver
_.____.
Omar
Receiver
Receiver
+
PD1
US RE41,294 E
PCK
u
PDQ
~_-
P01
+
Receiver
+
+
_____
Driver
+
+Receiver
_-_-—
Driver
Receiver
pCN __.‘ Driver
H
PCN
FIG. ‘I
US. Patent
Apr. 27, 2010
Sheet 10 0f 12
US RE41,294 E
Primary PCI Bus
PCI Clock
Asynchronous
T
1
PCI Bus
l0 Control
Hostrf
Controller
'me ace
Controller
XPBus
pLL
Controller
'
Clock
A A
XPBus _\ _ ~_ _
‘v
'
~‘l
pCK
PD[3::0]:
\
é
PCKR
: PDRBUO]
RSTEPti :
l
I
l
RSTEH”
Peripheral
#
lnlerfa ce
YY
Asynchronous
Controller
XPBUS
Controller
1
PLL
Clock
n’
PCI Bus
|(_)
Controller
Comm'
+
PCI Clock
+
{v
1
PCI
Secondary
PCl Bus
Device
FIG. l'O
US. Patent
xOm
Apr. 27, 2010
01
Sheet 12 0f 12
P01
mom
US RE41,294 E
mam
WWW
N_.OE
yoI u
01
wDl Q
NilQ
US RE41,294 E
1
2
PASSWORD PROTECTED MODULAR
COMPUTER METHOD AND DEVICE
a typewriter format. The keyboard also has the length and
width for easily inputting information by way of keys to the
computer. The mouse also has a su?icient siZe and shape to
Matter enclosed in heavy brackets [ ] appears in the
original patent but forms no part of this reissue speci?ca
another location.
tion; matter printed in italics indicates the additions
made by reissue.
Other types of computing devices include portable com
puting devices such as “laptop” computers and the like.
easily move a curser on the display from one location to
Although somewhat successful, laptop computers have
CROSS REFERENCE TO RELATED
APPLICATIONS
many limitations. These computing devices have poor dis
play technology. In fact, these devices often have a smaller
[The following two commonly-owned copending
?at panel display that has poor viewing characteristics.
Additionally, these devices also have poor input devices
such as smaller keyboards and the like. Furthermore, these
applications, including this one, are being ?led concurrently
and the other one is hereby incorporated by reference in their
entirety for all purposes:]
[1. US. patent application Ser. No. 09/183,816, William
devices have limited common platforms to transfer informa
tion to and from these devices and other devices such as PCs.
Up to now, there has been little common ground between
W. Y. Chu, entitled, “Modular Computer Security Method
and Device”. and]
[2. US. patent application Ser. No. 09/183,493, William
W. Y. Chu, entitled, “Password Protected Modular Computer
Method and Device”.]
these platforms including the PCs and laptops in terms of
upgrading, ease-of-use, cost, performance, and the like.
Many differences between these platforms, probably some
20
for the reissue of US. Pat. No. 6,321,335. The reissue appli
cations are application Ser. No. 10/963,825 ?led Oct. 12,
2004, application Ser. No. 11/474,256?led Jun. 23, 2006
(the present application), application Ser. No. 11/517,601
?led Sep. 6, 2006, and application Ser. No. 12/322, 858?led
top and laptop to have “total” computing power, where the
desktop serves as a “regular” computer and the laptop serves
25
Feb. 5, 2009, the present application being a continuation
reissue ofU.S. Pat. No. 6,321,335.
BACKGROUND OF THE INVENTION
30
The present invention relates to computing devices. More
particularly, the present invention provides a method and
device for securing a personal computer or set-top box using
password protection techniques. Merely by way of example,
the present invention is applied to a modular computing
environment for desk top computers, but it will be recog
niZed that the invention has a much wider range of applica
as a “portable” computer. Purchasing both computers is
often costly and runs “thousands” of dollars. The user also
wastes a signi?cant amount of time transferring software
and data between the two types of computers. For example,
the user must often couple the portable computer to a local
area network (i.e., LAN), to a serial port with a modem and
then manually transfer over ?les and data between the desk
top and the portable computer. Alternatively, the user often
must use ?oppy disks to “Zip” up ?les and programs that
35
bility. It can be applied to a server as well as other portable or
modular computing applications.
what intentional, has bene?ted computer manufacturers at
the cost of consumers. A drawback to having two separate
computers is that the user must often purchase both the desk
Notice: More than one reissue application has been ?led
40
Many desktop or personal computers, which are com
monly termed PCs, have been around and used for over ten
years. The PCs often come with state-of-art microprocessors
exceed the storage capacity of conventional ?oppy disks,
and transfer the ?oppy disk data manually.
Another drawback with the current model of separate por
table and desktop computer is that the user has to spend
money to buy components and peripherals the are duplicated
in at least one of these computers. For example, both the
desktop and portable computers typically include hard disk
drives, ?oppy drives, CD-ROMs, computer memory, host
processors, graphics, accelerators, and the like. Because pro
gram software and supporting programs generally must be
such as the Intel PentiumTM microprocessor chips. They also
include a hard or ?xed disk drive such as memory in the 45 installed upon both hard drives in order for the user to oper
giga-bit range. Additionally, the PCs often include a random
access memory integrated circuit device such as a dynamic
random access memory device, which is commonly termed
DRAM. The DRAM devices now provide up to millions of
memory cells (i.e., mega-bit) on a single slice of silicon. PCs
also include a high resolution display such as cathode ray
50
tubes or CRTs. In most cases, the CRTs are at least 15 inches
rate monitor, keyboard, mouse, and the like and is generally
incompatible with other desktop PCs. The docking station is
or 17 inches or 20 inches in diameter. High resolution ?at
panel displays are also used with PCs.
Many external or peripheral devices can be used with the
PCs. Among others, these peripherals devices include mass
storage devices such as a ZipTM Drive product sold by
ate programs on the road and in the o?ice, hard disk space is
often wasted.
One approach to reduce some of these drawbacks has
been the use of a docking station with a portable computer.
Here, the user has the portable computer for “on the road”
use and a docking station that houses the portable computer
for of?ce use. The docking station typically includes a sepa
55
also generally not compatible with portable computers of
other vendors. Another drawback to this approach is that the
portable computer typically has lower performance and
functionality than a conventional desktop PC. For example,
the processor of the portable is typically much slower than
processors in dedicated desktop computers, because of
Iomega Corporation of Utah. Other storage devices include
external hard drives, tape drives, and other. Additional
devices include communication devices such as a modem, 60
power consumption and heat dissipation concerns. As an
which can be used to link the PC to a wide area network of
computers such as the Internet. Furthermore, the PC can
include output devices such as a printer and other output
means. Moreover, the PC can include special audio output
devices such as speakers the like.
PCs also have easy to use keyboards, mouse input devices,
and the like. The keyboard is generally con?gured similar to
example, it is noted that at the time of drafting of the present
application, some top-of-the-line desktops include 400 MHZ
processors, whereas top-of-the-line notebook computers
65
include 266 MHZ processors.
Another drawback to the docking station approach is that
the typical cost of portable computers with docking stations
US RE41,294 E
3
4
can approach the cost of having a separate portable computer
and a separate desktop computer. Further, as noted above,
because different vendors of portable computers have pro
present invention is also implemented using conventional
technologies that can be provided in the present computer
prietary docking stations, computer users are held captive by
their investments and must rely upon the particular computer
vendor for future upgrades, support, and the like.
embodiment, one or more of these bene?ts can be available.
system in an easy and e?icient manner. Depending upon the
These and other advantages or bene?ts are described
throughout the present speci?cation and are described more
particularly beloW.
Thus What is needed are computer systems that provide
reduced user investment in redundant computer components
and provide a variable level of performance based upon
Well as its advantages and features, are described in more
computer con?guration.
detail in conjunction With the text beloW and attached FIGS.
These and other embodiments of the present invention, as
SUMMARY OF THE INVENTION
BRIEF DESCRIPTION OF THE DRAWINGS
According to the present invention, a technique including
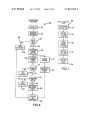
FIG. 1 is a simpli?ed diagram of a computer system
according to an embodiment of the present invention;
FIG. 2 is a simpli?ed diagram of a computer module
according to an embodiment of the present invention;
FIG. 3 is a simpli?ed side-vieW diagram of a computer
module according to an embodiment of the present inven
a method and device for securing a computer module using a
passWord in a computer system is provided. In an exemplary
embodiment, the present invention provides a security sys
tem for an attached computer module (“ACM”). In an
embodiment, the ACM inserts into a Computer Module Bay
(CMB) Within a peripheral console to form a functional
computer.
20
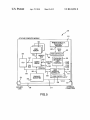
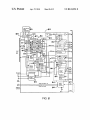
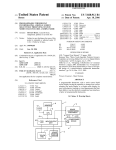
FIG. 4 is a simpli?ed layout diagram of a security system
In a speci?c embodiment, the present invention provides a
computer module. The computer module has an enclosure
for a computer system according to an embodiment of the
present invention;
that is insertable into a console. The module also has a cen
tral processing unit (i.e., integrated circuit chip) in the enclo
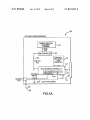
FIG. 5 is a simpli?ed block diagram of a security system
25
sure. The module has a hard disk drive in the enclosure,
for a computer module according to an embodiment of the
present invention; and
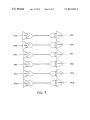
FIGS. 6 and 7 shoW simpli?ed ?oW diagrams of security
Where the hard disk drive is coupled to the central processing
unit. The module further has a programmable memory
device in the enclosure, Where the programmable memory
device can be con?gurable to store a passWord for prevent
ing a possibility of unauthorized use of the hard disk drive
tion;
30
methods according to embodiments of the present invention.
FIG. 8 is a detailed block diagram ofone embodiment of
and/or other module elements. The stored passWord can be
the host interface controller (HIC) of the present invention.
FIG. 9 is a schematic diagram ofthe signal lines PCK,
any suitable key strokes that a user can change from time to
time. In a further embodiment, the present invention pro
PDO to PD3, and PCN.
vides a permanent passWord or user identi?cation code
35
stored in ?ash memory, Which also can be in the processing
unit, or other integrated circuit element. The permanent
passWord or user identi?cation code is designed to provide a
permanent “?nger print” on the attached computer module.
In a speci?c embodiment, the present invention provides a
variety of methods. In one embodiment, the present inven
tion provides a method for operating a computer system such
40
I. System HardWare
includes inserting an attached computer module (“ACM”)
45
microprocessor unit (e.g., microcontroller, microprocessor)
coupled to a mass memory storage device (e.g., hard disk).
The method also includes applying poWer to the computer
system and the ACM to execute a security program, Which is
stored in the mass memory storage device. The method also
and PDO to PD3.
DESCRIPTION OF SPECIFIC EMBODIMENTS
as a modular computer system and others. The method
into a bay of a modular computer system. The ACM has a
FIG. I0 is a block diagram ofanother embodiment ofthe
HIC and PIC ofthepresent invention and the interface ther
ebetween.
FIG. I] is a detailed block diagram ofanother embodi
ment ofthe HIC ofthe present invention.
FIG. I2 is a schematic diagram ofthe signal lines PCK
FIG. 1 is a simpli?ed diagram of a computer system 1
according to an embodiment of the present invention. This
diagram is merely an illustration and should not limit the
scope of the claims herein. One of ordinary skill in the art
Would recognize other variations, modi?cations, and altema
tives. The computer system 1 includes an attached computer
50
includes prompting for a user passWord from a user on a
module (i.e., ACM) 10, a desktop console 20, among other
elements. The computer system is modular and has a variety
display (e.g., ?at panel, CRT). In a further embodiment, the
of components that are removable. Some of these compo
present method includes a step of reading a permanent pass
nents (or modules) can be used in different computers,
Word or user identi?cation code stored in ?ash memory, or
other integrated circuit element. The permanent passWord or
user identi?cation code provides a permanent ?nger print on
the attached computer module. The present invention
includes a variety of these methods that can be implemented
in computer codes, for example, as Well as hardWare.
Numerous bene?ts are achieved using the present inven
Workstations, computerized television sets, and portable or
55
laptop units.
In the present embodiment, ACM 10 includes computer
components, as Will be described beloW, including a central
processing unit (“CPU”), IDE controller, hard disk drive,
60
computer memory, and the like. The computer module bay
(i.e., CMB) 40 is an opening or slot in the desktop console.
tion over previously existing techniques. The present inven
tion provides mechanical and electrical security systems to
The CMB houses the ACM and provides communication to
and from the ACM. The CMB also provides mechanical pro
prevent theft or unauthorized use of the computer system in
tection and support to ACM 10. The CMB has a mechanical
a speci?c embodiment. Additionally, the present invention
substantially prevents accidental removal of the ACM from
the console. In some embodiments, the present invention
prevents illegal or unauthorized use during transit. The
65
alignment mechanism for mating a portion of the ACM to
the console. The CMB further has thermal heat dissipation
sinks, electrical connection mechanisms, and the like. Some
details of the ACM can be found in co-pending patent appli
US RE41,294 E
6
5
cation Nos. 09/149,882 and 09/149,548 ?led Sep. 8, 1998,
1) A CPU With cache memory;
2) Core logic device or means;
commonly assigned, and hereby incorporated by reference
for all purposes.
In a preferred embodiment, the present system has a secu
rity system, Which includes a mechanical locking system, an
5
electrical locking system, and others. The mechanical lock
ing system includes at least a key 11. The key 11 mates With
key hole 13 in a lock, Which provides a mechanical latch 15
in a closed position. The mechanical latch, in the closed
position, mates and interlocks the ACM to the computer
module bay. The mechanical latch, Which also has an open
position, alloWs the ACM to be removed from the computer
module bay. Further details of the mechanical locking sys
tem are shoWn in the Fig. beloW.
FIG. 2 is a simpli?ed diagram of a computer module 10
according to an embodiment of the present invention. This
diagram is merely an illustration and should not limit the
scope of the claims herein. One of ordinary skill in the art
user passWord;
6) Operating System, application softWare, data ?les on
primary HDD;
7) An interface device and connectors to peripheral con
sole;
8) A softWare controllable mechanical lock, lock control
5
means, and other accessories.
The ACM connects to a peripheral console With poWer
supply, a display device, an input device, and other elements.
Some details of these elements With the present security sys
tem are described in more detail beloW.
FIG. 4 is a simpli?ed layout diagram of a security system
Would recogniZe other variations, modi?cations, and alterna
tives. Some of the reference numerals are similar to the pre
3) Main memory;
4) A single primary Hard Disk Drive (“HDD”) that has a
security program;
5) Flash memory With system BIOS and programmable
20
for a computer system according to an embodiment of the
vious Fig. for easy reading. The computer module 10
includes key 11, Which is insertable into keyhole 13 of the
present invention. This diagram is merely an illustration and
lock. The lock has at least tWo position, including a latched
or closed position and an unlatched or open position. The
latched position secures the ACM to the computer module
bay. The unlatched or open position alloWs the ACM to be
inserted into or removed from the computer bay module. As
shoWn, the ACM also has a slot or opening 14, Which alloWs
nary skill in the art Would recogniZe other variations,
should not limit the scope of the claims herein. One of ordi
modi?cations, and alternatives. The layout diagram illus
25
components (e.g., Host Interface Controller) are depicted in
dashed lines. The layout diagram has a ?rst portion, Which
includes a central processing unit (“CPU”) module 400, and
the latch to move into and out of the ACM. The ACM also
has openings 17 in the backside for an electrical and/or
mechanical connection to the computer module bay, Which
is connected to the console.
FIG. 3 is a simpli?ed side-vieW diagram of a computer
module according to an embodiment of the present inven
tion. This diagram is merely an illustration and should not
limit the scope of the claims herein. One of ordinary skill in
trates the top-vieW of the module 10, Where the backside
30
a second portion, Which includes a hard drive module 420. A
common printed circuit board 437 houses these modules and
the like. Among other features, the ACM includes the central
processing unit module 400 With a cache memory 405,
Which is coupled to a north bridge unit 421, and a host inter
35
face controller 401. The host interface controller includes a
lock control 403. As shoWn, the CPU module is disposed on
a ?rst portion of the attached computer module, and couples
the art Would recogniZe other variations, modi?cations, and
to connectors 17. Here, the CPU module is spatially located
alternatives. Some of the reference numerals are similar to
near connector 17.
the previous FIG. for easy reading. As shoWn, the ACM
module inserts into the computer module bay frame 19,
The CPU module can use a suitable microprocessing unit,
40
Which is in the console. A side 27 and a bottom 19 ofACM
slide and ?t ?rmly into the computer module bay frame,
microcontroller, digital signal processor, and the like. In a
speci?c embodiment, the CPU module uses, for example, a
400 MHZ Pentium II microprocessor module from Intel Cor
Which has at least a bottom portion 19 and back portion 26.
A backside 23 of the ACM faces backside 26 of the frame.
poration and like microprocessors from AMD Corporation,
ACM also has a front-side or face 25 that houses the lock
and exposes the keyhole 13 to a user. The key 11 is insertable
Corporation), and others. In other aspects, the microproces
from the face into the keyhole.
As the ACM inserts into the frame, connector 17 couples
and inserts into connector 21. Connector 17 electrically and
mechanically interface elements of the ACM to the console
through connector 21. Latch 14 should be moved aWay from
the bottom side 19 of the module bay frame before inserting
the ACM into the frame. Once the ACM is inserted fully into
the frame, latch 15 is placed in a closed or lock position,
Where it keeps the ACM ?rmly in place. That is, latch 15
biases against a backside portion 29 of the ACM enclosure to
hold the ACM in place, Where the connector 17 ?rmly
engages, electrically and mechanically, With connector 21.
Alpha Chip, Apple Computer Corporation PoWerPC G3
To remove the ACM, latch 15 is moved aWay or opened from
the back side portion of the ACM enclosure. ACM is manu
Cyrix Corporation (noW National Semiconductor
sor can be one such as the Compaq Computer Corporation
50
processor, and the like. Further, higher speed processors are
contemplated in other embodiments as technology increases
in the future.
In the CPU module, host interface controller 401 is
coupled to BIOS/?ash memory 405. Additionally, the host
interface controller is coupled to a clock control logic, a
con?guration signal, and a peripheral bus. The present
55
invention has a host interface controller that has lock control
403 to provide security features to the present ACM.
Furthermore, the present invention uses a ?ash memory that
includes codes to provide passWord protection or other elec
60
tronic security methods.
The second portion of the attached computer module has
ally pulled out of the computer module bay frame, Where
the hard drive module 420. Among other elements, the hard
connector 17 disengages With connector 21. As shoWn, the
key 11 is used to selectively move the latch in the open or
locked position to secure the ACM into the frame module.
drive module includes north bridge 421, graphics accelerator
In most embodiments, the ACM includes an enclosure
such as the one described With the folloWing components,
Which should not be limiting:
65
423, graphics memory 425, a poWer controller 427, an IDE
controller 429, and other components. Adjacent to and in
parallel alignment With the hard drive module is a personal
computer interface (“PCI”) bus 431, 432. A poWer regulator
435 is disposed near the PCI bus.
US RE41,294 E
7
8
In a speci?c embodiment, north bridge unit 421 often
couples to a computer memory, to the graphics accelerator
423, to the IDE controller, and to the host interface controller
via the PCI bus. Graphics accelerator 423 typically couples
memory device or devices such as dynamic random access
memory (“DRAM”) integrated circuits and others. The
DRAM includes at least 32 Meg. or 64 Meg. and greater of
memory, but can also be less depending upon the applica
tion. Alternatively, the main memory can be coupled directly
With the CPU in some embodiments. The north bridge also
couples to a graphics subsystem 515 via bus 542. The graph
ics subsystem can include a graphics accelerator, graphics
memory, and other devices. Graphics subsystem transmits a
video signal to an interface connector, Which couples to a
to a graphics memory 423, and other elements. IDE control
ler 429 generally supports and provides timing signals nec
essary for the IDE bus. In the present embodiment, the IDE
controller is embodied as a 643U2 PCI-to IDE chip from
CMD Technology, for example. Other types of buses than
IDE are contemplated, for example EIDE, SCSI, 1394, and
the like in alternative embodiments of the present invention.
The hard drive module or mass storage unit 420 typically
display, for example.
includes a computer operating system, application software
program ?les, data ?les, and the like. In a speci?c
embodiment, the computer operating system may be the
WindoWs98 operating system from Microsoft Corporation
hard disk drive that serves as a main memory unit for pro
of Redmond Wash. Other operating systems, such as
WindoWsNT, MacOS8, Unix, and the like are also contem
plated in alternative embodiments of the present invention.
Further, some typical application softWare programs can
The attached computer module also includes a primary
grams and the like. The hard disk can be any suitable drive
that has at least 2 GB and greater. As merely an example, the
hard disk is a Marathon 2250 (2.25 GB, 2 1/2 inch drive)
product made by Seagate Corporation of Scotts Valley, but
can be others. The hard disk communicates to the north
20
include O?ice98 by Microsoft Corporation, Core1 Perfect
Suite by Corel, and others. Hard disk module 420 includes a
hard disk drive. The hard disk drive, hoWever, can also be
replaced by removable hard disk drives, read/Write CD
ROMs, ?ash memory, ?oppy disk drives, and the like. A
small form factor, for example 2.5", is currently
contemplated, hoWever, other form factors, such as PC card,
and the like are also contemplated. Mass storage unit 240
may also support other interfaces than IDE. Among other
features, the computer system includes an ACM With secu
rity protection. The ACM connects to the console, Which has
25
device 505 With a BIOS. The ?ash memory device 505 also
has codes for a user passWord that can be stored in the
device. The ?ash memory device generally permits the stor
30
at least the following elements, Which should not be limiting.
1) Connection to input devices, e. g. keyboard or mouse;
2) Connection to display devices, eg Monitor;
3) Add-on means, eg PCI add-on slots;
35
4) Removable storage media subsystem, e.g. Floppy
drive, CDROM drive;
5) Communication device. eg LAN or modern;
6) An interface device and connectors to ACM;
7) A computer module bay With a notch in the frame for
ACM’s lock; and
40
507 communications to the north bridge via bus 535 and host
PCI bus. The host interface controller also has a lock control
509, Which couples to a lock. The lock is attached to the
controller 507 communicates to the console using bus 511,
Which couples to connection 513.
In one aspect of the present invention the security system
uses a combination of electrical and mechanical locking
mechanisms. Referring to FIG. 5A, for example, the present
45
module bay provides mechanical support and protection to
ACM. The module bay also includes, among other elements,
a variety of thermal components for heat dissipation, a frame
the provides connector alignment, and a lock engagement,
Which secures the ACM to the console. The bay also has a
printed circuit board to mount and mate the connector from
the ACM to the console. The connector provides an interface
betWeen the ACM and other accessories.
FIG. 5 is a simpli?ed block diagram 500 of a security
system for a computer module according to an embodiment
age of such passWord Without a substantial use of poWer,
even When disconnected. As merely an example, the ?ash
memory device has at least 4 Meg. or greater of memory, or
16 Meg. or greater of memory. A host interface controller
module and has a manual override to the lock on the host
interface controller in some embodiments. Host interface
8) PoWer supply and other accessories.
As noted, the computer module bay is an opening in a
peripheral console that receives the ACM. The computer
bridge by Way of a hard disk drive controller and bus lines
502 and 531. The hard disk drive controller couples to the
north bridge by Way of the host PCI bus, Which connects bus
537 to the north bridge. The hard disk includes computer
codes that implement a security program according to the
present invention. Details of the security program are pro
vided beloW.
The attached computer module also has a ?ash memory
50
55
of the present invention. This diagram is merely an illustra
system provides a lock status mechanism in the host inter
face controller 509. The lock status of the lock is determined
by checking a lock status bit 549, Which is in the host inter
face controller. The lock status bit is determined by a signal
553, Which is dependent upon the position of the lock. Here,
the position of the lock is closed in the ground 559 position,
Where the latch couples to a ground plane in the module
and/or system. Alternatively, the signal of the lock is at Vcc,
for example, Which is open. Alternatively, the signal can be
ground in the open position and Vcc in the closed position,
depending upon the application. Other signal schemes can
also be used depending upon the application.
Once the status is determined, the host interface controller
tion and should not limit the scope of the claims herein. One
turns the lock via solenoid 557 in a lock on or lock off
of ordinary skill in the art Would recogniZe other variations,
position, Which is provided through the control bit 551, for
example. The control bit is in a register of the host interface
modi?cations, and alternatives. The block diagram 500 has a
variety of features such as those noted above, as Well as
60
others. In the present diagram, different reference numerals
are used to shoW the operation of the present system.
The block diagram is an attached computer module 500.
The module 500 has a central processing unit, Which com
municates to a north bridge 541, by Way of a CPU bus 527.
The north bridge couples to main memory 523 via memory
bus 529. The main memory can be any suitable high speed
controller in the present example. By Way of the signal
schemes noted and the control bit, it is possible to place the
lock in the lock or unlock position in an electronic manner.
Once the status of the lock is determined, the host interface
controller can either lock or unlock the latch on the module
65
using a variety of prompts, for example.
In a preferred embodiment, the present invention uses a
passWord protection scheme to electronically prevent unau